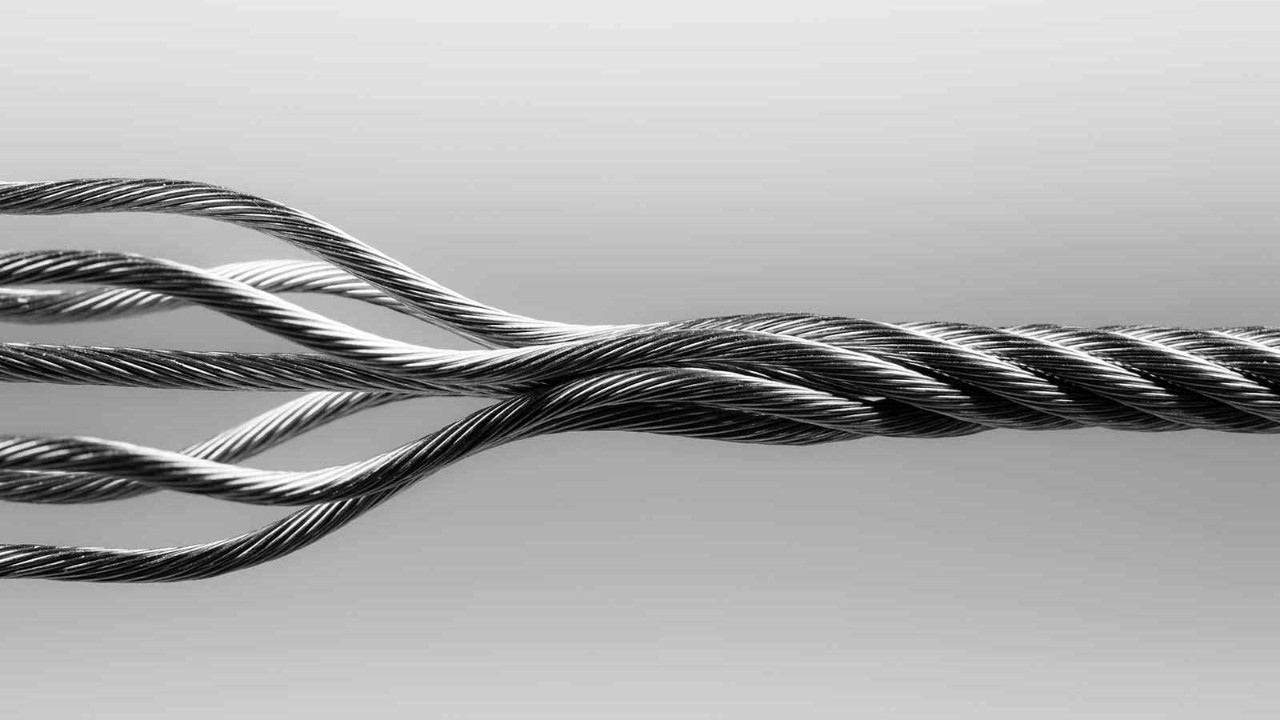
Beyond the technology and resources dedicated to strengthening cybersecurity and limiting risks, companies are increasingly adopting a ‘zero-trust’ approach that represents an important shift in mentality.
Zero trust, which means eliminating trust in digital interactions, is a crucial mindset to help combat cyber risks. Implementing the approach requires particular skillsets among staff and, more importantly, holistic support from the company.
‘The concept of zero trust has been at the heart of the approach to managing sensitive client data’
Essentially, it means keeping network doors and windows closed and locked at all times, and opening them up only when needed and then closing them again quickly.
‘Accounting firms have long been used to remote working, due to client site-based projects. As a result, the concept of zero trust has been at the heart of the approach to managing sensitive client data,’ says Richard Watson, global and Asia-Pacific cybersecurity consulting leader at EY.
As accounting and finance professionals are increasingly working online, in part out of necessity due to the pandemic, the zero-trust approach has emerged as an important block of effective defences to combat the growing number of cyber risks.
‘It builds a defence that is ‘perimeter-less,’ alongside protection and trust measures for every aspect of connected networks, devices and other resources,’ says Henry Shek, head of technology consulting – cyber security at KPMG Hong Kong.
Shift in mindset
Adopting the zero-trust approach may require a shift in corporate and personal mindset.
‘The first principle of the approach for accounting professionals is to remove any implicit trust from digital security systems,’ says Watson. ‘Staff should pivot from a “trust but verify” mindset to a “never trust, always verify” one.’
As important as this mindset is, however, it is not enough.
A zero-trust architecture is an integrated approach to securing enterprise data and resources, and ‘it encompasses identity (personal and non-personal entities), credentials and access management,’ says Marcos Mistretta, a consultant at PwC Spain.
‘Staff should pivot from a “trust but verify” mindset to a “never trust, always verify” one’
In practical terms, this means that particular skillsets and specific knowledge are needed among staff.
A solid understanding of data regulations such as the European Union’s General Data Protection Regulation (GDPR) and the ISO 27001 standard of cybersecurity can be useful in protecting data.
On the technical side, ‘professional experience in systems and network deployment are essential elements, and staff should know about border security systems, such as firewalls, intrusion detection systems (IDS) and intrusion prevention systems (IPS),’ says Rafa Tenorio, cyber intelligence and incident management/response service coordinator at cybersecurity consulting firm Bidaidea, headquartered in Spain.
Familiarity with identity and access management, as well as network security, can help employees push the zero-trust approach further, says Kok Tin Gan, cybersecurity and privacy partner at PwC Hong Kong. It is also important to know the management of standards and frameworks, such as the US National Institute of Standards and Technology (NIST), which can help accounting professionals implement the right approach, adds Mistretta.
Ongoing process
Zero trust is a good way to protect a company from cyber risks, but it is not an approach that can be adopted or implemented overnight. Rather it should be part of an ongoing digital transformation process.
‘It is unrealistic to assume that you already have zero trust in place by purchasing a solution. It is a gradual evolution with incremental improvements, gaining visibility into risk and implementing measures,’ says Mistretta.
‘It is unrealistic to assume that you already have zero trust in place by purchasing a solution’
Companies should always have holistic plans and keep their objectives in mind when they start implementing a zero-trust approach. The best practice for the zero-trust model is where ‘the network is always assumed to be hostile and all communication is secured regardless of network location,’ says Watson.
‘Every device, user, network, and data flow is authenticated and authorised. Any access to resources is granted on a per-session basis,’ he adds.
To achieve this, it is better to ‘set up a joint business and security team to analyse zero-trust objectives for the organisation,’ says Shek.
‘This includes validating the objectives of the zero-trust programme, mapping out what information and applications need to be accessed and by whom, determining how to enable trust today and tomorrow, finding out how the workforce and customer demands are changing, and then linking all of these to the digital transformation journey,’ he explains.
Multiple measures
That said, implementation may vary from one company to another. Large companies already on their digital transformation journeys are likely to be better placed to take on a zero-trust approach as some factual findings are already in place, says Shek.
‘Measures such as multi-factor identification, network segmentation and information inventory, together with data flows, are already in place,’ he says.
Finally, companies that are not yet ready can still embark on the journey as part of their digital transformation plan and improve their cyber security by applying measures that work for them.
Cybersecurity approaches
The zero-trust approach is not the only way to mitigate cybersecurity risks, nor is it effective on its own.
‘Effective practices are not monolithic. The awareness of users is vital to combat cyber risks. Implementing single sign-on (SSO) and multi-factor authentication (MFA) solutions, and being able to monitor, isolate and control all devices that are connected to the network at any given time can all help us reduce risks,’ says Antonio Camacho, account manager at ALSO-IREO in Spain.
‘Another effective practice to combat cyber risks is to follow a Security by Design approach to safeguard trust,’ says Richard Watson, global and Asia-Pacific cybersecurity consulting leader at EY.
‘This is a proactive, pragmatic and strategic approach that considers risk and security at the start of any new initiative, and nurtures trust at every stage. This allows organisations to take on more risk, lead transformational change and innovate with confidence, knowing there is no bow wave of security issues to be addressed at the end of the project.’
More information
See also AB’s special edition on skills